Have you ever wondered what would happen if a single corrupted file brought your operations to a halt or if…
Want to take your brand overseas? Well, most organizations dream of it, and something that helps them turn it into…
The current state of business today is the silent revolution. The world’s most successful companies quietly deploy astonishing efficiencies with…
Would you believe us if we told you that by the time you finish reading this post, more than 50…
Zero Trust operates on the belief that no one can automatically be trusted. Actually, no one gets access to your…
Getting a disk write error on Steam while downloading or updating a game is frustrating; there is no doubt about…
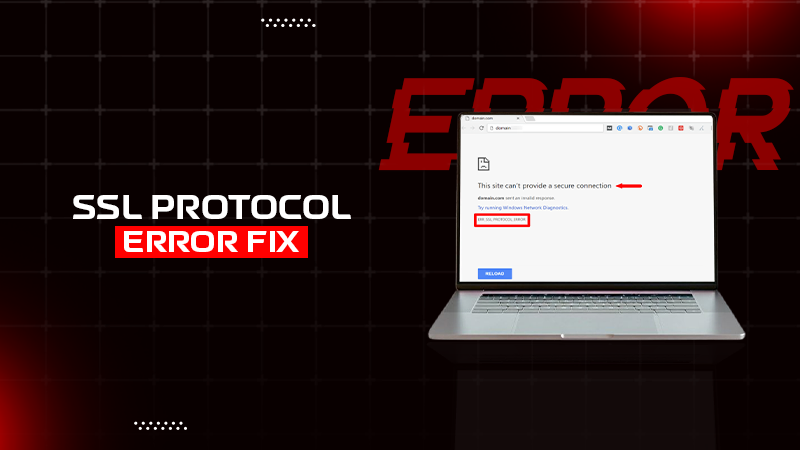
Have you ever clicked on a website and got a message saying – “ERR_SSL_PROTOCOL_ERROR”? Wondering what it means? This usually…
Who doesn’t want to increase the rate of satisfied customers for their business? Customers are honestly the lifeline of every…
Error code 429 is the most infamous HTTP issue that pops up when you hit the already set limit for…