In today’s highly volatile environment, businesses face many critical cyber threat challenges, including the impact of advanced ransomware attacks. Relying…
Businesses today must use technology. Unfortunately, there is no way around this. Failure to incorporate technology into business operations can…
Most data breaches do not begin with a hoodie-wearing hacker. The story begins with mundane events, such as an unattended…
The decision to purchase software is no longer straightforward. Licenses are replaced by subscriptions, features are layered behind tiers, and…
We can safely assume that, for a variety of reasons, people in our world spend a significant amount of time…
Every day, businesses generate huge volumes of data – yet identifying what truly needs improvement and what should be focused…
You don’t know how much you rely on your laptop until it acts up. The cursor stops moving. The fan…
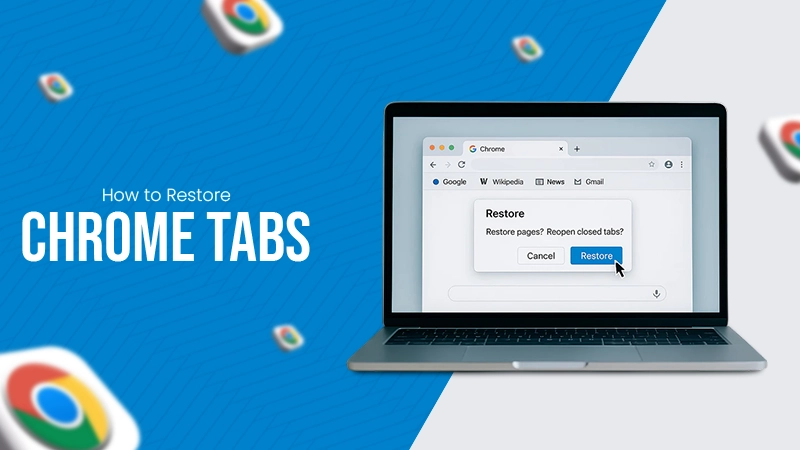
Imagine this: You are juggling ten things—one tab for work, one for shopping, and one for that article you wanted…
The majority of engineering teams work at a much slower pace than they could because of systematic friction in their…