We can safely assume that, for a variety of reasons, people in our world spend a significant amount of time…
Every action within your systems – let it be logins, errors or updates – creates a log. Most of these…
Every day, businesses generate huge volumes of data – yet identifying what truly needs improvement and what should be focused…
Most enterprises do not struggle due to the lack of data but because they fail to manage it properly. And…
A few years back, marketing advice was all about instinct and guess work. Experience mattered; creativity ruled. And, yes, these…
Extracting data from websites shouldn’t feel like solving a Rubik’s Cube blindfolded. Yet for many businesses, web scraping remains frustratingly…
Supply chain systems are all about accuracy. Because even the slightest error can reflect on a series of tasks: one…
Data is no longer a byproduct of business; it is the business. With every click on an e-commerce site, organizations…
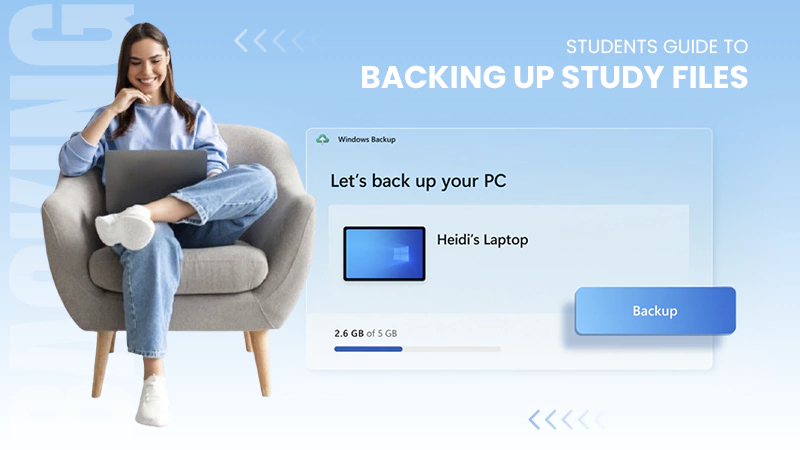
You don’t know how much you rely on your laptop until it acts up. The cursor stops moving. The fan…