Because they lack the human context to identify and piece together complex errors such as business logic errors, authorization bypasses, or subtle cloud misconfigurations that span multiple layers of the application.
Why Pentesting Is a Core Part of Modern DevSecOps
- Don't wait, just read this comprehensive guide right away!
- What DevSecOps Covers, and the Gap Pentesting Closes
- Where Pentesting Fits in a DevSecOps Lifecycle
- What Pentesters Actually Find that Matters to DevSecOps
- How to Operationalize Pentesting inside DevSecOps
- Tooling Synergy, Scanners Plus Humans
- Building a Measurable Program
- Choosing a Pentest Partner That Fits DevSecOps
- Conclusion
- Frequently Asked Questions

Software is shipped continuously, attackers are getting faster, and simple application scanning does not catch design flaws or chained exploits. Recent reports show a rise in exploited vulnerabilities while many organizations cannot patch their systems quickly.
An analysis done in 2025 indicated that a substantial portion of breaches were tied to vulnerability exploitation, and a lot were weaponized within 24 hours of being disclosed. In this climate, penetration testing services can provide DevSecOps teams a real picture of business risk.
This article will discuss where pentesting fits in the pipeline, what it catches that tools do not, and how to operationalize the findings so that you can ship software in a secure way while not slowing delivery.
Don’t wait, just read this comprehensive guide right away!
KEY TAKEAWAYS
- Pentesting Closes the Automation Gap.
- It is a strategic, layered process that occurs in the pipeline.
- This prioritizes issues based on their actual impact on critical assets, guiding development teams to fix what matters most.
- To integrate pentesting into DevSecOps, findings must be formatted as actionable items with steps assigned to specific code owners with clear SLA tags for remediation.
What DevSecOps Covers, and the Gap Pentesting Closes
Modern DevSecOps integrates developer-owned security with continuous tooling, for example SAST, IAST, SCA, DAST, and secret scanning in CI. These automate detection of known patterns, yet they rarely validate exploitability across architectural trust boundaries, multiple weaknesses, and misconfigurations. Pentesting closes that gap by simulating chaining issues, real adversaries, and confirming impact on data, money, or uptime.
Why Scanners Miss Things
- Business logic flaws and broken workflows
- Chained misconfigurations across identity, cloud, and app layers
- Context heavy risks like authorization bypass or critical data exposure
- Secrets in the wild that trigger live compromise paths, even after a clean code scan
Where Pentesting Fits in a DevSecOps Lifecycle
Pentesting is a strategic process, which includes several steps. Use a layered approach that matches delivery cadence.
1. Plan and Design
- Map important user journeys and data flows.
- Threat model new features.
- Align with the NIST Secure Software Development Framework, SSDF, to set results based controls from day one.
2. Build and Integrate
- Run SCA, SAST, and secret scanning on each PR, block merges on high risk findings.
- Pilot IAST on high value services to check runtime issues early. In parallel, schedule targeted pentest sprints on features that shifts trust boundaries, like new payment flows or admin portals.
3. Test in Staging
- Execute scenario based pentests that chain app, identity, API, and cloud misconfigurations.
- Validate fixes, then export tickets with reproduction steps and risk ratings.
4. Release and Operate
- Conduct attack surface reviews and lightweight DAST on every release.
- Add continuous pentesting bursts during peak risk moments, for instance after major refactors or dependency upgrades.
5. Learn and Improve
- Track mean time to remediate, false positive rate, exploited path reductions, and regression rates.
- Update your SSDF system library and playbooks after each engagement.
What Pentesters Actually Find that Matters to DevSecOps
Broken Access Control dominates modern web risk. Skilled testers instantly pivot from a unit IDOR or role bypass to full account takeover or data exfiltration. Cryptographic failures and insecure design still appear, particularly where cloud and app assumptions clash. Pentests validate vulnerability and prioritize what to fix first.
Real World Data Supports This
- Vulnerability exploitation as an initial access vector rose year over year in 2025 DBIR analysis.
- More than 39 million secrets were identified by GitHub secret scanning in 2024, a strong signal that secret hygiene is a live risk, not a theory.
How to Operationalize Pentesting inside DevSecOps
You may get stuck while operationalizing Pentesting inside DevSecOps. So, check out the things you can do:
Make Findings Ticket Friendly
- Format: title, CVE or CWE, affected asset, business impact, steps to reproduce, exploit proof, screenshots or PoC, and fix guidance.
- Assign: route to the code owners or platform team with SLA tags.
- Automate: create CI checks that validate the fix or add unit tests for the vulnerable path.
Set Cadences That Match Risk
- Quarterly focused pentests for flagship products.
- Pre-release pentests for high risk features.
- Continuous retesting for critical auth flows, using the same payloads to prevent regressions.
Integrate with SSDF Outcomes
SSDF expects result based practices, not just tools. Maintain an internal checklist that maps each pentest finding to your SSDF controls for design, testing, coding, and release, including AI components if relevant. NIST’s 800-218A adds concrete instructions for generative AI and model supply chain risk.
Tooling Synergy, Scanners Plus Humans
- SAST plus pentest: SAST flags risky patterns, testers prove exploitability and prioritize.
- DAST plus pentest: DAST sweeps broad surfaces, testers chain subtle logic flaws.
- Secret scanning plus pentest: scanning finds leaked keys, testers verify lateral movement and blast radius.
- Cloud posture plus pentest: CSPM lists misconfigs, testers traverse network, identity, and data paths to crown jewels.
Building a Measurable Program
Building a measurable program is a step by step process. There you can, track a small, meaningful set of KPIs:
- Mean time to remediate, MTTR for criticals
- Exploit to fix ratio per release
- Recurring flaw rate per team or service
- Aligned to CISA KEV where applicable, exploit window from disclosure to patch,
- Business impact avoided, for example blocked fraud or protected revenue
Several 2025 analyses tie breach growth to slower patching and smooth weaponization. Measure and shrink that window with targeted pentesting sprints and enforced SLAs.
Choosing a Pentest Partner That Fits DevSecOps
Look for vendors who provide developer ready findings, retests included, and who work in your sprint rhythm. Explore a manual, human powered service that integrates directly with your issue tracker and CI, if you want a practitioner led approach.
Review an industry roundup of leading providers for a deeper look at the market and methodology patterns. You can also review and compare services in this detailed research:
Check for: Top Penetration Testing Companies 2025.
Conclusion
DevSecOps succeeds when security is consistent, measurable, and tied to business risk. Pentesting is the human in the loop that turns tool output into exploit proof, reduces exploit windows, developer ready fixes, and validates that your controls work under real pressure. Align to SSDF, blend scanners with expert testing, and ship with confidence.
Frequently Asked Questions
Why can’t automated scanners replace penetration testing?
When should we use pentesting in the DevSecOps lifecycle?
Strategic pentesting should be used throughout the entire lifecycle, including threat modeling in the planning phase.
What is the most common high-risk finding from a pentest?
Access control breaches continue to be one of the most serious and common risks.
What is the most important metric to track for a most comprehensive program?
Mean Time to Remedy (MTTR) is the most important metric to track for a most comprehensive program, required for significant findings.
Most people think hackers need advanced tools to find security gaps. Sorry to break the news, but sometimes, Google is…
If you are a part of any business, you might have attended meetings. And in case you were connected to…
SSD data recovery software can retrieve data that has been deleted, damaged, or otherwise rendered inaccessible from the SSD hard…
How can I improve the performance and grow my business? My team is already occupied with several projects, how do…
It feels very frustrating to lose all your digital data due to just one panic mistake of selecting a password…
Special Purpose Vehicles (SPVs) are a type of legally structured company. They are created by parent companies, usually with temporary…
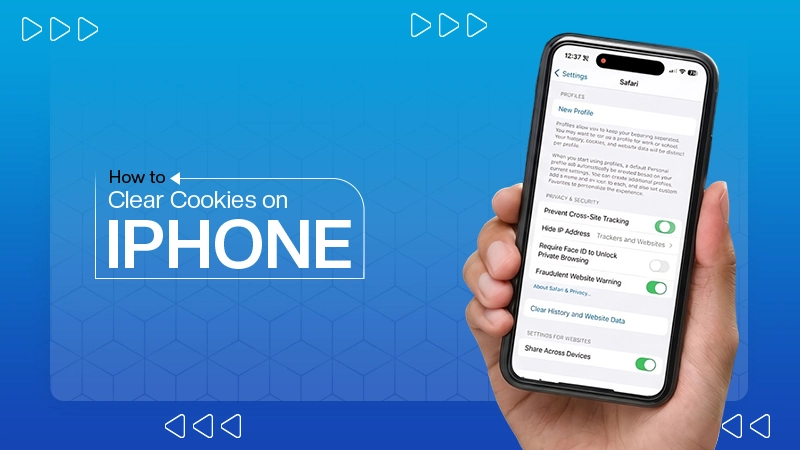
Web cache and cookies make browsing faster by saving logins, settings, and site data. But over time, they can slow…
Finding the best tools for your company feels like a big job. You need systems that actually help your team…
In the digital age, instant messaging apps have become an essential part of our daily communication. Whether for personal use,…