It’s the Department of Defense cybersecurity certification framework designed to ensure defense contractors properly protect sensitive government information.
CMMC Compliance Is Coming for Manufacturers. Here Is What You Need to Do

“Cybersecurity is much more than a matter of IT.” — Stephane Nappo (Cybersecurity Professional)
For manufacturers working within the defense supply chain, that quote has become a business reality. Cybersecurity is no longer just an internal technical concern. It now directly determines whether your company can win, renew, or retain Department of Defense contracts.
CMMC 2.0 compliance is moving from guidance to enforcement, with the Department of Defense making its position increasingly clear: companies that fail to meet certification requirements risk losing access to defense-related work entirely. For manufacturers that depend on federal contracts or subcontracting relationships, the question is no longer if compliance matters. It is whether your organization can become compliant before contract requirements catch up with you.
In this guide, I’ll tell you what manufacturers need to do, common compliance gaps, timelines, costs, and how to prepare before contracts are affected.
KEY TAKEAWAYS
- CMMC 2.0 compliance is becoming mandatory for manufacturers working with the Department of Defense supply chain.
- Most manufacturers handling Controlled Unclassified Information must meet 110 NIST SP 800-171 security controls.
- Common compliance gaps include shared accounts, weak access controls, poor logging, and outdated systems.
- Starting with a gap assessment early can prevent rushed implementations, contract loss, and costly remediation later.
The Clock Is Ticking
If your manufacturing company holds Department of Defense contracts or if you are a subcontractor to someone who does, CMMC 2.0 compliance is no longer a future concern. It’s code red now. The Department of Defense has made it clear: no certification, no contract. And the enforcement timeline that seemed distant two years ago is now arriving.
CMMC requires defense contractors to meet specific cybersecurity standards based on the sensitivity of information they handle. Level 1 covers basic cyber hygiene. Level 2, which applies to most manufacturers handling Controlled Unclassified Information, requires compliance with 110 security controls from NIST SP 800-171. Level 3 is reserved for the most sensitive programs and adds expert-level protections.
Why Michigan Manufacturers Are Especially Exposed
Michigan houses 17,000+ manufacturing companies, many of which are in defense. Automotive suppliers, tooling companies, precision machine shops, and electronics manufacturers supporting military programs are all likely to fall under CMMC requirements.
The challenge is that most of these companies built their IT systems for production efficiency, not cybersecurity compliance. Shop floor networks, legacy equipment running outdated operating systems, and shared login credentials are common across the industry. These are not just bad habits. Under CMMC, they are disqualifying deficiencies.
What makes this particularly urgent is the flow-down requirement. If a prime contractor needs CMMC Level 2 certification, every subcontractor in the chain that touches CUI must also be certified. This means small machine shops with 20 employees are held to the same cybersecurity standards as billion-dollar defense primes.
The 110 Controls That Stand Between You and Your Contracts
NIST SP 800-171 organizes its 110 security controls into 14 categories covering areas such as:
- Access control
- Incident response
- System monitoring
- Data protection
For most manufacturers, the gaps tend to cluster in a few predictable areas.
Access control is usually the first problem. Shared accounts on shop floor computers, a lack of multi-factor authentication, and admin privileges given to employees who do not need them are nearly universal. Audit and accountability are next. Most manufacturers have no logging infrastructure, which means they cannot prove who accessed what information and when. Media protection, which governs how CUI is stored on portable devices and how it is destroyed, is another common gap.
Good news: these gaps are fixable. Bad news: they take time. Most manufacturers need half to a year to acquire full CMMC readiness, which is why starting with a managed network security assessment is critical. You need to know exactly where you stand before you can build a realistic timeline.
What a Realistic CMMC Roadmap Looks Like
The first step is a gap assessment. This maps your current security posture against the 110 NIST 800-171 controls and produces a Plan of Action and Milestones that documents exactly what needs to change. This document is not optional. Assessors will ask for it.
Step two remediation takes most of the time and budget. You will likely need to implement multi-factor authentication, deploy endpoint detection and response tools, set up proper logging and monitoring, create and test an incident response plan, and establish formal policies for data handling. Depending on your starting point, this phase can take three to nine months.
Step three is the formal assessment. For Level 2, this requires assessment from a Certified Third-Party Assessment Organization. Until C3PAOs are fully ramped up, some companies may be able to self-assess, but the expectation is moving firmly toward independent verification.
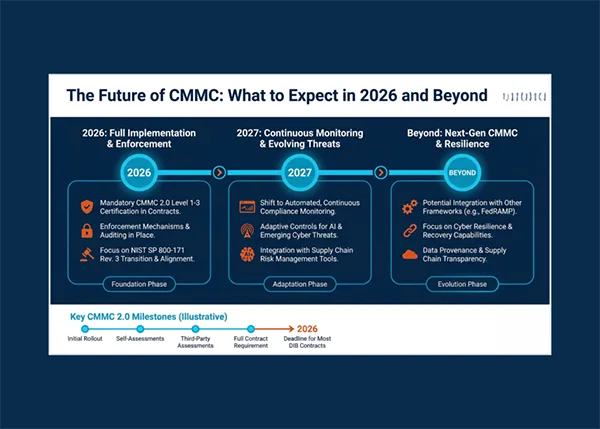
The infographic presents the present and future of CMMC:
The Cost of Doing Nothing
Some manufacturers continue to assume enforcement delays will buy them more time. Or that their prime contractors will not enforce flow-down requirements. This is a losing bet. Primes are already including CMMC requirements in new contracts. Even, several have started auditing their supply chains independently.
Losing a defense contract is obvious. But a cybersecurity incident involving CUI triggers mandatory reporting to the Department of Defense. The reputational damage and potential legal liability from a breach of controlled information can be existential for a small manufacturer.
The manufacturers who will come through this transition in the best shape are the ones treating CMMC not as a compliance checkbox, but as an opportunity to modernize their IT operations. The security controls required by CMMC overlap significantly with what any well-run business should have in place. Companies that invest in managed cybersecurity services with built-in compliance support end up with more reliable systems, better disaster recovery, and stronger competitive positioning, regardless of whether they are bidding on defense work.
Start Now. Not Next Quarter.
If your business comes under CMMC and you haven’t done anything, immediately start scheduling a gap assessment. Know where you stand. Build your plan. Give yourself enough runway to get certified before your contracts require it.
The companies that wait until a contract renewal forces their hand will find themselves scrambling, overpaying for rushed implementations, and potentially losing work to competitors who prepared earlier. In manufacturing, you would never start production without a plan. Treat your cybersecurity the same way.
Conclusion
CMMC compliance is no longer on the horizon. For defense manufacturers, it is quickly becoming a baseline requirement for staying competitive and protecting future revenue.
The organizations that act early will have more time to strengthen systems, train employees, and approach certification strategically rather than reactively. In an industry built on precision and reliability, cybersecurity preparedness is rapidly becoming part of the standard.
Frequently Asked Questions
What is CMMC 2.0?
Which manufacturers need CMMC compliance?
Any manufacturer directly working with the Department of Defense or subcontracting within the defense supply chain may need compliance, especially if they handle Controlled Unclassified Information (CUI).
How long does CMMC preparation usually take?
Most manufacturers require between six and twelve months to fully prepare for certification, depending on their current cybersecurity maturity.
What happens if a company fails to achieve compliance?
Failure to meet required CMMC standards can result in lost contracts, inability to bid on future defense work, reputational damage, and increased legal or cybersecurity risks.
Making a presentation doesn’t just mean designing slides. It’s about defining a clear structure, using defined logic, useful visuals, and…
Businesses with poor queue management see return customer rates of 62%, while those with excellent queue management see rates of…
Competitor research without traffic data is guesswork. You can guess who your rivals are, guess how big they are, guess…
The performance of digital business is directly related to website speed, uptime, and scalability. Slow page performance has a negative…
“People work for money but go the extra mile for recognition, praise, and rewards.” — Dale Carnegie (Writer & Teacher)…
Almost every company that depends on data runs into the same problem: although they can find the data they need,…
Financial data supports every part of a business, directly affecting cash flow, payroll, tax reports, audits, customer billing, and daily…
Learning has transformed in the modern age with the integration of new technologies to help students and professionals prosper in…
Marketing teams and other professionals feel like SEO, reels and digital ads are the only way to do marketing. This…