A company requires the assistance of a technological specialist to deal with cyber threats, data recovery, cloud migration, and to create an IT strategy for their business.
Top 7 Technology Consultant Services Every Data-Driven Business Needs (2026)
- 1. Vendor-Neutral Technology Advisors (like CommQuotes)
- 2. Cybersecurity Consultants (like CrowdStrike Services)
- 3. Data Backup and Disaster Recovery Specialists (like Veeam)
- 4. Cloud Migration and Infrastructure Consultants (like Accenture)
- 5. IT Strategy and Planning Advisors (like Gartner Advisory)
- 6. Managed Service Providers (like ConnectWise)
- 7. Digital Transformation Consultants (like IBM Consulting)
- The Right Consultant Makes All the Difference
- Frequently Asked Questions

Data loss isn’t just an IT inconvenience. It is a threat to the survival of a business. Research shows that 40% of businesses do not reopen after facing such a disaster.
This is why organizations need to plan for the future, instead of remaining reactive and taking actions only after a crisis forces their hand. Taking assistance from technology consultants changes that equation entirely.
Whether your firm is dealing with ransomware, hardware, failure, or something else, here are the seven best consultancy services every business needs to fix these issues.
Key Takeaways
- Vendor-Neutral tech solutions with CommQuotes
- Dealing with cyber threats and vulnerability management with incident responses
- Creating backup systems and recovering data with test backup architectures
- Transforming businesses with the best modern digital platforms to improve efficiency
1. Vendor-Neutral Technology Advisors (like CommQuotes)
Advisors specialising in vendor-neutral technology handle processes between vendors and businesses, cutting through the sales pressure to match clients with suitable and genuine solutions.
CommQuotes is one of the best technology consultants operating in this space — a vendor-neutral platform connecting organizations with more than 450 managed service and telecom providers at no cost to the client.
Having helped more than 6,800 businesses save $54.9 million while managing over $100 million in contracts, CommQuotes delivers measurable value without a fee, making it the most efficient starting point for any data-driven business evaluating its technology stack.
2. Cybersecurity Consultants (like CrowdStrike Services)
Ransomware and cyberattacks are among the leading causes of irreversible data loss. Cybersecurity consultants assess vulnerabilities, implement layered defenses, and build compliance frameworks aligned with HIPAA, SOC 2, and GDPR standards.
CrowdStrike Services offer incident responses alongside threat detection and elimination, combining reactive and preventive coverage in a single engagement.
With 236.1 million ransomware incidents recorded in the first half of 2022 alone and an average 16-day recovery window for victims, this expertise is not optional for organizations that handle sensitive data.
3. Data Backup and Disaster Recovery Specialists (like Veeam)
Backup systems are only as reliable as their last successful test — yet 58% of backups fail during recovery due to outdated technology or malware.
These disaster management specialists design, implement, and test backup architectures to close dangerous gaps and ensure that recovery objectives are met when a crisis occurs.
Veeam, for instance, supports hybrid environments spanning on-premises and cloud workloads. For organizations managing structured databases, a dedicated SQL database recovery tool can serve as a critical last line of defense when conventional backup layers fall short.
Interesting Fact
Data recovery specialists once successfully recovered 99% of the data from a hard drive that survived the Challenger space shuttle disaster
4. Cloud Migration and Infrastructure Consultants (like Accenture)
Moving workloads to the cloud introduces risks that many organizations underestimate — 85.6% of reported data loss incidents now occur in cloud environments.
Cloud consultants guide businesses through migration while correctly configuring the shared responsibility model, ensuring both the cloud provider and the client know exactly what they are protecting.
Accenture’s cloud practice, for example, pairs migration execution with security architecture reviews to prevent the misconfigurations that most commonly lead to exposure.
5. IT Strategy and Planning Advisors (like Gartner Advisory)
IT advisors help businesses build strategies aligning with technological investments that support long-term goals covering infrastructure, storage, and data recovery planning..
Gartner Advisory, for instance, provides sector-specific benchmarks that allow leadership teams to prioritize spending based on risk exposure rather than intuition.
Organizations running Windows environments should ensure their recovery roadmap explicitly accounts for Windows data and partition recovery scenarios, which differ significantly from cloud-native recovery processes and require purpose-built tooling.
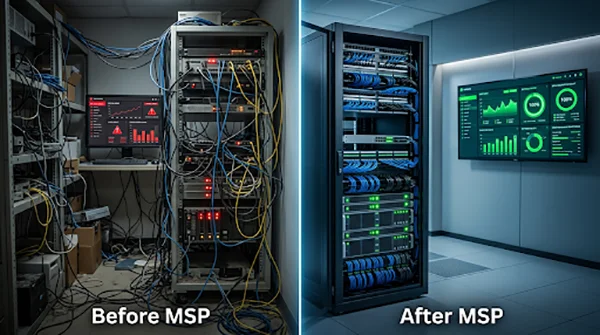
6. Managed Service Providers (like ConnectWise)
Managed Service Providers offer continuous IT monitoring, maintenance, and proactive support — functioning as an outsourced IT department.
This ongoing vigilance is particularly valuable for businesses without in-house IT staff, as it catches hardware failures, software corruption, and security anomalies before they escalate into data loss events.
ConnectWise, for example, powers MSP operations for thousands of providers globally.
According to the IBM Cost of a Data Breach Report, organizations with extensive security AI and automation save an average of $1.76 million per breach compared to those without — a gap that proactive MSP engagement helps close.
7. Digital Transformation Consultants (like IBM Consulting)
Digital transformation consultants help businesses adopt AI, automation, analytics, and modern platforms to improve efficiency and competitive positioning.
These engagements usually require transferring legacy data, and a misstep during the platform transition process can cause permanent data loss.
IBM Consulting, for example, brings sector-specific transformation roadmaps that account for data governance from the outset rather than treating it as an afterthought.
Only 27% of companies report that their technology is fully aligned with their business objectives, illustrating how significant the execution gap remains.

The Right Consultant Makes All the Difference
The organizations that recover fastest from these data failures and disasters are rarely the ones that respond well. They are the ones who prepared well.
Whether your priority is cybersecurity, cloud infrastructure, disaster recovery, or digital transformation, engaging the right specialist before a crisis occurs is the most cost-effective investment your organization can make.
Assess your current IT consulting setup today, and treat your data not as a byproduct of operations but as the critical asset it truly is.
Frequently Asked Questions
Why does a company require the services of a technology consultant?
What are the risks associated with a mismanaged cloud migration?
A mismanaged transfer of data between clouds can cause permanent data loss of important data saved in the cloud.
What is the need for an IT strategy?
An IT strategy needs to be designed to deal with future threats and risks that may impact the business’s operations and functions significantly.
How is a digital transformation useful for a business?
A digital transformation involves the adoption of modern platforms that integrate with legacy systems of a company, automating many processes and easing the workflow and operations of a firm.
Businesses with poor queue management see return customer rates of 62%, while those with excellent queue management see rates of…
Competitor research without traffic data is guesswork. You can guess who your rivals are, guess how big they are, guess…
The performance of digital business is directly related to website speed, uptime, and scalability. Slow page performance has a negative…
“People work for money but go the extra mile for recognition, praise, and rewards.” — Dale Carnegie (Writer & Teacher)…
Almost every company that depends on data runs into the same problem: although they can find the data they need,…
Financial data supports every part of a business, directly affecting cash flow, payroll, tax reports, audits, customer billing, and daily…
“Cybersecurity is much more than a matter of IT.” — Stephane Nappo (Cybersecurity Professional) For manufacturers working within the defense…
Learning has transformed in the modern age with the integration of new technologies to help students and professionals prosper in…
Marketing teams and other professionals feel like SEO, reels and digital ads are the only way to do marketing. This…