A crucial step to enhance the quality of network access is to implement strong password policies, which help provide access to only authorised users.
From Planning to Protection: Enhancing Network Speed and Security
Tired of the frozen screens and security breaches in your systems that lead to delayed tasks and surpassed deadlines. Don’t worry, the solution is here.
Delayed work, lost deals, misplaced data, and constant frustration if the computers of your office put you in the mentioned conditions, then it is not just the system but also the network responsible for this condition.
So, if you are facing similar issues and need to figure out how to get out of this problem. Read further to know how to cope with these conditions.

Key Takeaways
- Installing next-generation firewalls, unified threat management, and more to have a harmonious technology.
- Building a micro-segmentation and continuous monitoring mindset to speed up as well as the security of systems
- Building the core idea around practical and necessary questions to have a clear road map
- Including redundancy and quality of service for good performance.
Planning with Purpose
You wouldn’t build a house without a blueprint, yet so many networks evolve haphazardly.
But an effective network enhancement starts with a clear-eyed assessment of your current reality and future needs.
This isn’t just about buying the fastest router on the market; it’s about understanding the soul of your network: the data.
A solid plan answers fundamental questions:
- What is the load? How many devices are actually connecting, and what are they doing? A single 4K video stream consumes vastly more bandwidth than a thousand email checks.
- Where is the data going? Is most of your traffic staying inside the office (local), heading to the cloud (SaaS applications), or going out to the general internet?
- What are the crown jewels? Which servers hold your customer data, financial records, or proprietary research? These need to be in the most fortified, fastest-access part of your network.
Architecting for Performance and Resilience
Today’s network is a living thing, as it has to flex for mobile teams and cloud apps while staying solid where it counts, so a simple blueprint cannot cater to all those requirements.
A strong network leans on non-negotiables such as :
- Segmentation keeps your critical data isolated from risky guest Wi-Fi.
- Redundancy eliminates single points of failure, automatically rerouting traffic when hardware fails.
- And Quality of Service plays traffic cop, prioritizing video calls over large downloads so your critical apps never lag.
Leveraging Expert Partnerships: For many organizations, the complexity of modern networking makes it impractical to go it alone.
This is where partnering with a provider who specializes in secure enterprise networking services becomes a strategic advantage.
By offloading the heavy lifting to managed service providers or utilizing advanced cloud-based platforms, companies gain access to enterprise-grade firewalls, intrusion detection, and optimized routing.
This approach brings baked-in protection and high-speed connectivity to the table without requiring a massive, on-site team of experts.
The Modern Security Mindset: Zero Trust
Implementing a Zero Trust architecture transforms how speed and security interact:
- Micro-segmentation: We take segmentation to the extreme. Workloads are isolated down to the individual application level. This means even if an attacker breaches one part of the network, they can’t move laterally to find more valuable data.
- Least Privilege Access: Users are given access only to the specific data and applications they need to do their jobs, and nothing more. This shrinks the attack surface dramatically.
- Continuous Monitoring: Authentication isn’t a one-time event at login. The network constantly monitors behavior. If a user suddenly tries to download an entire database at 3:00 AM, the session is automatically terminated, regardless of who they logged in as.
Technology in Harmony
You can have the most brilliant strategy in the world, but without the right tools, it’s just a theory. Today’s tech actually lets security and speed work together.
The real trick is avoiding the trap of buying a bunch of disconnected gadgets that end up fighting each other. Instead, go for tools like :
- Next-Generation Firewalls (NGFW): These aren’t your grandfather’s firewalls. They’re smart enough to look at the actual application trying to get through, like knowing the difference between a Zoom call and a random ad tracker, and can prioritize or block accordingly.
- Unified Threat Management (UTM): Perfect for smaller teams. Instead of juggling five different security tools, UTM bundles everything: firewall, antivirus, VPN, into one tidy appliance that’s actually manageable.
- Secure Access Service Edge (SASE): This one’s a lifesaver for remote teams. It wraps networking and security into a single cloud service, so your people working from coffee shops get fast, secure access without routing everything through headquarters first.

Cultivating a Culture of Vigilance
Technology is a shield, but the people holding it need to know how to use it.
Enhancing network speed and security isn’t just an IT project; it’s a cultural shift.
Building this human firewall is the last, critical piece of the puzzle:
- Regular Training: Move beyond the boring, annual compliance video. Use engaging, real-world simulations to teach staff how to spot social engineering attempts.
- Clear Policies: Make policies easy to understand. Explain why they shouldn’t use the same password for everything or plug in an unknown USB drive.
- Open Communication: Create an environment where people feel comfortable reporting a mistake (like clicking a bad link) immediately, without fear of punishment. The speed of that report can be the difference between a minor incident and a major breach.
From the initial blueprint to the daily habits of every user, enhancing network speed and security is a continuous cycle of planning, protection, and adaptation.
By weaving them together, we build a network that is not only fast and safe but truly resilient.
Conclusion
It is the active planning, well-built roadmaps, and important qualities such as micro-segmentation, monitoring, and quality of service that ensure the network speed and security are enhanced.
Building an enhanced network is vital for a business because it helps in meeting deadlines, closing deals, and allows the utilisation of time well.
Frequently Asked Questions
What is the crucial step that enhances the security of network access control?
What causes slow network performance?
The health of your system affects the internet connection; this means that if your computer has viruses or spyware, it can lead to reduced speed.
What does it mean when a network has reduced security?
The primary reason for a network to have weak security is a weakly secured router; the router here does not refer to the provider’s network but to your home /office.
What are the three elements of network security?
The three core elements of network security are: confidentiality, integrity, and availability, which ensure a smooth working network.
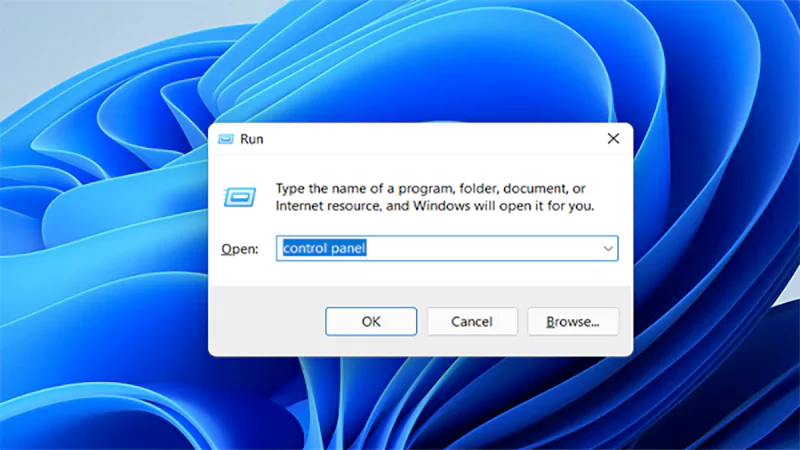
The control panel in Windows is a collection of tiny programs. It is used to configure the various aspects of…
How do you remove applications from a Mac? Most Mac users think there is just one way to delete apps.…
Many tech platforms, ad networks, SaaS tools, and online stores in the world have critical traffic and infrastructure that require…
In the corporate conversation around information, most of the firms are scared of losing data. That’s understandable, as most of…
Touchscreen on a Chromebook sounds great until it starts getting in the way. Accidental taps while typing, smudges, and random…
Ever blocked someone on your iPhone and later found yourself wondering if you can see blocked texts on iPhone? It…
Architecture decisions are fundamental to ensuring steady growth in any business or technical step, especially when the topic is laying…
Every small business or growing team needs to deal with a common issue—the database that was working perfectly for the…
Nowadays, IT conversations jump straight to cloud apps, wireless coverage, and cybersecurity tools. While these are visible and easy to…