VSaaS is a cloud-based service that looks for security gaps and configuration problems in network applications and systems.
How Cloud Services Manage Data in Vulnerability Scanning as a Service (VSaaS)
Businesses these days are highly dependent on servers, applications, APIs, databases, and cloud platforms. However, something that they might miss is that every piece of that infrastructure can potentially contain vulnerabilities. And cybercriminals are constantly on the hunt for such weak points.
Even Verizon’s Data Breach Investigations Report consistently found that many breaches begin with known vulnerabilities that were never patched. In simpler terms, the biggest threats are often not the unknown attacks but their known weaknesses that are left unaddressed.
This is where cloud-powered vulnerability scanning services emerge as an effective solution. In this guide, learn how they continuously monitor systems and analyze potential risks, helping organizations stay ahead of the evolving cyber threats while protecting their sensitive data.
Key Takeaways
- Vulnerability Scanning as a Service (VSaaS) helps businesses find unsecure gateways before hackers can use them.
- Cloud infrastructure makes it possible to keep an eye on security all the time across complicated systems.
- Secure data collection, storage, and processing keep private information safe during scans.
- VSaaS works best when it is used with backup and disaster recovery plans.
- Finding vulnerabilities before they happen makes cybersecurity defenses much stronger.
What is Vulnerability Scanning as a Service (VSaaS)
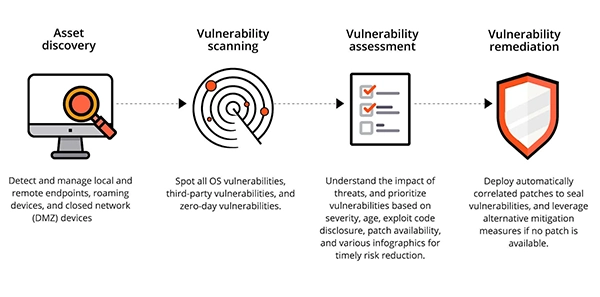
Vulnerability Scanner as a Service (VSaaS) is a cloud-based security solution that scans systems, applications, and networks to detect security weaknesses automatically. Typically, it analyzes systems for outdated software versions, missing security patches, misconfigured servers, exposed ports and services, and known digital vulnerabilities.
These scanners can compare system configurations against large databases of known threats and security flaws. The result is a detailed report that helps security teams prioritize fixes before attackers discover the same weaknesses.
Role of Cloud Infrastructure in Data Security Scanning
Systems need computational power and flexibility to scan large, complex environments, and cloud platforms provide exactly that. Organizations can run continuous scans across networks, applications, and cloud services.
Data Collection
Gathering data is the first step to vulnerability scanning. Scanning tools collect relevant data such as operating system details, installed applications, network configurations, and open ports and services. All this allows the scanning engine to identify potential security gaps in the system.
Data Storage
Once the required data is collected, it is stored in cloud environments for analysis and reporting safely. Cloud platforms allow organizations to maintain historical scan records, making it easier to track vulnerabilities over time and measure improvements in security posture.
Secure Data Processing
Cloud-based engines then process the data to compare configurations against vulnerability datasets. These datasets are constantly updated to include newly discovered security threats. This ensures that scanning systems remain current and capable of detecting emerging vulnerabilities.
How Cloud Services Handle Sensitive Data During Scans
Cloud services may come across sensitive client data while analyzing it. And to safeguard that, cloud platforms implement strict policies and strategies. Such as,
- Encryption during data transmission
- Encrypted storage for scan results
- Access control policies
- Audit logs and activity monitoring
Many modern services also rely on acontinuous vulnerability scanner that runs in the background and identifies new risks as they evolve.
H2: Benefits of Cloud-Based Vulnerability Scanning for Businesses
Cloud-based VSaaS solutions offer several advantages over traditional security tools.
- First, they eliminate the need for expensive on-premise security infrastructure. The cloud provider manages scanning tools, updates vulnerability databases, and maintains the platform.
- Second, they let you see security risks in real time across networks and apps.
- Third, they are easy to scale. Cloud scanners can quickly grow to cover new infrastructure as businesses grow and add new systems.
A lot of businesses also use Cloud Managed IT Services along with VSaaS. This lets security monitoring, vulnerability scanning, and infrastructure all work together in one place.
FUN FACT
Cybersecurity researchers discover thousands of new vulnerabilities every year, which is why vulnerability databases are updated constantly
Integration of VSaaS with Data Backup and Recovery Systems
Vulnerability scanning is an important way to protect an organization’s digital assets, but it is not the only thing that is done. It works best when used with other security measures. Many businesses rely on backup and disaster recovery services with VSaaS platforms.
If there is a cyberattack or a system breach because of a weakness, backup services will be able to get the data back without losing it. This approach makes resilience stronger by combining threat detection, watching for vulnerabilities, backups that are safe, ability to recover quickly.
When used together, these systems make it harder for modern cyber threats to get through.
Final Considerations
Cyber threats are always changing; businesses can’t just do security checks every now and then. Therefore, modern cybersecurity strategies include continuous monitoring, automated scanning, and proactive vulnerability detection as standard features.
Cloud-based VSaaS solutions make this possible by giving you infrastructure that can grow with your business, real-time data, and tools for identifying threats faster.
Vulnerability scanning is not just a security feature for businesses that depend on digital systems; it is also a crucial way to protect sensitive data and keep operations running smoothly.
Frequently Asked Questions
What is Vulnerability Scanning as a Service (VSaaS)?
How often should vulnerability scans be performed?
Many businesses run automated scans every week or all the time to find new security holes quickly, and this is considered the ideal interval.
Does scanning for vulnerabilities reveal private information?
Encryption, strict access controls, and a secure cloud infrastructure are all used by reputable services to keep scan data safe.
Is VSaaS good for small businesses?
Yes. Cloud-based scanning solutions are easy to use and can be used by small businesses as well.
“Photography is the story I fail to put into words.” — Destin Sparks (Landscape Photographer) For years, Lightroom presets have…
A website’s performance is mainly determined by its Speed. Even a slight delay can reduce conversions by a significant margin.…
“People influence people. Nothing influences people more than a recommendation from a trusted friend.” — Mark Zuckerberg (Meta CEO) That…
Artificial intelligence has evolved from a mere tool to the cornerstone of advancements in the new era. Over the years,…
“If everyone is moving forward together, then success takes care of itself.” — Henry Ford (Industrialist & Business Magnate) Handoffs…
Healthcare executives are under pressure to protect patient safety, clinician time, and data privacy while modernizing the delivery of care.…
Locked out of your Android phone or stuck on the screen? It happens more than you think. A forgotten PIN,…
Switching from Android to iPhone should not feel like rebuilding your life from scratch. Restoring contacts on iPhone should be…
Even though the DSP segment is the largest market within AdTech at the moment, an ad server remains a crucial…



